Configuring the system for FIPS 140-3
To switch modes, first log in to the core node and then:
1. Stop all core services: stop ALL
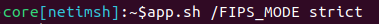
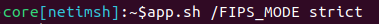
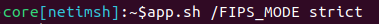
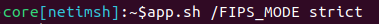
2. Execute: app.sh /FIPS_MODE <mode>
3. Start all core services: start ALL
For example: to switch to strict mode run:
Strict FIPS mode
About the other swarm nodes
No specific action needs to be taken to configure the other swarm nodes. However, once Common Services start, the FIPS mode change will be pushed to the swarm and all instances of the following services will automatically restart to apply the updated FIPS mode:
• cisco-aci-poller
• hyperion-connector
• meraki-poller
• net-auditor
• notification-sender
• poller
• portal-proxy-service
• ssh-jumphost
• streaming-telemetry-import
• telemetry-telegraf
• viptela-poller
• wmi-poller
Any other service not listed above will not restart. These services are always FIPS 140-3 compliant.
Potential issues when enabling FIPS 140-3 support
When using off mode, NetIM will behave like previous versions with no noticeable impact on cryptographic operations.
However, enabling strict mode may lead to communication issues with some remote devices or services. These issues typically involve failures to authenticate or establish secure connections and are more likely to occur with older devices or systems that do not support FIPS 140-3. Problem areas might include:
• Polling devices
• Collecting data
• External authentication (e.g., LDAP, RADIUS)
• Any secure communication with external systems
If you experience these issues after switching to strict mode, consider reverting to off mode to confirm whether FIPS restrictions are the cause.